Rapid7: The Story of Vulnerability Management's Cloud Pivot
I. Introduction and Episode Roadmap
In early 2026, a cybersecurity company that once commanded a market capitalization north of eight billion dollars trades for roughly four hundred and fifty million. Its stock, which peaked near one hundred and forty-five dollars a share in November 2021, now hovers around six dollars. The company generates nearly eight hundred and sixty million dollars in annual revenue, employs thousands of security professionals worldwide, and protects some of the most sensitive networks on the planet. Its name is Rapid7, and its story is one of the most instructive cautionary tales in enterprise software.
This is a company that did almost everything the playbook demands. It started with a killer product in vulnerability scanning. It made one of the shrewdest acquisitions in cybersecurity history when it bought the open-source Metasploit penetration testing framework. It went public at the right time. It pivoted to the cloud. It built a multi-product platform. It acquired companies to fill portfolio gaps. And yet, despite all of that execution, it finds itself in 2026 fighting for relevance, squeezed between cloud-native upstarts that never carried legacy baggage and platform behemoths like CrowdStrike and Palo Alto Networks that can bundle security into massive, take-it-or-leave-it deals.
The central question of the Rapid7 story is one that haunts every enterprise software company built in the early 2000s: How do you survive an architectural shift that makes your original product category almost unrecognizable? Think about what vulnerability scanning meant in 2000. You had a network. It had a boundary, a perimeter. You put a scanner inside that boundary, pointed it at your servers and workstations, and it told you what was broken. Simple, elegant, necessary. Now fast-forward to 2026, where enterprise workloads run across three cloud providers, applications are built from thousands of microservices deployed in containers that live for minutes, and the very concept of a "network perimeter" is a relic of a bygone era. The product category that Rapid7 helped build has been stretched, fragmented, and reconstituted into something barely recognizable.
Microsoft pulled it off with Azure. Adobe pulled it off with Creative Cloud. But for every Microsoft, there are dozens of companies that attempted the cloud transition and either got acquired, went private, or simply faded. Rapid7's journey through all three of those possibilities, simultaneously, makes it a fascinating case study.
The story moves through three major inflection points. First, the Metasploit acquisition in 2009, which transformed Rapid7 from a competent but unremarkable scanner company into a brand that security practitioners genuinely respected. Second, the cloud platform rebuild starting around 2015, when the company bet its future on the Insight Platform and tried to evolve from a point solution into a comprehensive security analytics company. And third, the period from 2022 onward, when the stock collapsed, private equity came calling, activist investors took positions, and the company faced the most existential questions about its future since its founding.
Along the way, we will examine what vulnerability management actually means and why it matters, how the economics of cybersecurity companies differ from other software businesses, and what Rapid7's trajectory reveals about the structural forces shaping enterprise security in the 2020s. The lessons here apply far beyond a single company. They illuminate the fundamental tension between innovation and legacy, between depth and breadth, and between the relentless pace of technological change and the stubborn reality that enterprise customers move slowly.
II. The Early 2000s Security Landscape and Founding
Picture Boston in the summer of 2000. The NASDAQ had already begun its stomach-churning descent from the dot-com peak. Startups were burning through their last rounds of funding, and the words "business model" had suddenly become fashionable again. But in the corners of the technology world focused on security, something different was happening. The internet's explosive growth during the late 1990s had wired together millions of networks that were never designed to be connected, and the consequences were becoming terrifyingly clear. Love Bug, Code Red, Nimda, the worms were arriving faster than patches could be written. Security was no longer a luxury. It was becoming a survival requirement.
Into this environment stepped three co-founders: Alan Matthews, Chad Loder, and Tas Giakouminakis. They incorporated Rapid7 on July 10, 2000, in Boston. The name itself tells a story. "Rapid" conveyed speed, the urgency of finding vulnerabilities before attackers did. The "7" referred to the seven layers of the OSI networking model, a framework that breaks network communication into seven layers from physical cables up to application software. It was a technical nod that signaled these founders understood how networks actually worked at a fundamental level, not just the surface layer where users click buttons, but all the way down to the protocols that move packets across wires. Legend has it that much of the company's early planning happened on the Boston commuter rail, the three founders sketching out architectures and business plans during their daily rides into the city, scribbling on notepads and debating product features as commuters dozed around them.
Their founding thesis was straightforward but powerful: vulnerability management, the practice of systematically scanning networks to find security weaknesses before attackers exploit them, was being done poorly and expensively. The incumbents at the time, companies like Internet Security Systems and foundational tools like Nessus, served large enterprises but left the vast middle market underserved. Matthews, Loder, and Giakouminakis believed they could build a better scanner, sell it to a broader market, and grow into the space as cybersecurity spending inevitably increased.
Then came September 11, 2001, and the security landscape shifted permanently. Cybersecurity went from a technical concern to a national security priority overnight. The government began mandating security standards. Sarbanes-Oxley, enacted in 2002, created compliance requirements that forced publicly traded companies to think about their information systems in entirely new ways. HIPAA was tightening its grip on healthcare data. The Payment Card Industry Data Security Standard, PCI DSS, would soon mandate vulnerability scanning for any organization handling credit card data. A compliance-driven gold rush was underway.
The era of "checkbox security" arrived, organizations buying security tools not because they deeply understood the threat landscape, but because auditors required them to demonstrate that they had vulnerability scanning in place. A CISO could walk into a board meeting, show a vulnerability scan report, and check a box. Whether anyone actually fixed the vulnerabilities was, in many organizations, an afterthought. This was both a blessing and a limitation for companies like Rapid7. The compliance boom created enormous demand, but it also conditioned buyers to think about security as a procurement exercise rather than an operational imperative. It is a dynamic that persists to this day, though the sophistication of both threats and regulatory requirements has increased dramatically.
Rapid7's first significant product milestone came in 2004 with the launch of Nexpose, a vulnerability management tool that could scan enterprise networks, identify misconfigured systems, find unpatched software, and produce prioritized reports for security teams. Nexpose was solid engineering. It automated what had previously been a laborious manual process and delivered results in a format that security teams could actually act on. The product found its market quickly, particularly among mid-market companies that needed enterprise-grade scanning without enterprise-grade complexity or cost.
Boston's emerging technology ecosystem provided fertile ground. The city's deep bench of university talent from MIT, Harvard, and the surrounding research institutions created a pipeline of engineers who understood both the theoretical and practical dimensions of network security. Rapid7 was not yet a category leader, but it was building something real, a business with genuine technical merit, growing revenue, and a customer base that valued what the product delivered. By the middle of the decade, the company was generating tens of millions in revenue and had established itself as a credible player in the vulnerability management market. But credible was not the same as exceptional, and Rapid7's founders knew that the company needed something more to break through the noise. That something arrived in 2009, in the form of a hacker named HD Moore and a project called Metasploit.
III. The Metasploit Acquisition: A Defining Moment
On October 21, 2009, Rapid7 announced what would become the most consequential decision in the company's history: the acquisition of the Metasploit Project. To understand why this mattered so profoundly, you need to understand what Metasploit was and what it represented in the security community.
HD Moore, born Haroon David Moore, created Metasploit in 2003. Originally written in Perl and later rewritten in Ruby, Metasploit was an open-source penetration testing framework, essentially a toolkit that allowed security professionals to simulate real attacks against their own networks.
Think of it this way. Imagine you own a building and you want to know if it is secure. A vulnerability scanner is like a building inspector who walks through the hallways, checks the locks, looks at the windows, and hands you a report that says "the lock on the third-floor fire escape is weak, and the basement window doesn't close properly." Useful information, certainly. But Metasploit is different. Metasploit is the team that actually tries to pick that lock, climb through that window, and walk out with the contents of your safe. It does not just identify theoretical weaknesses. It proves them exploitable. The difference between knowing you have a vulnerability and knowing an attacker can actually use it to compromise your systems is enormous, and Metasploit bridged that gap in a way no other tool could match.
By 2009, Metasploit had become the single most widely used penetration testing tool in the world, with hundreds of thousands of users and a vibrant community of contributors who were constantly adding new exploits, modules, and capabilities. It was used by everyone from government intelligence agencies to small consulting firms running security assessments for local businesses.
Here is what made Metasploit remarkable from a business perspective. Moore and a loose network of volunteer contributors had built and maintained this entire project essentially on nights and weekends. There was no full-time development team. There was no company behind it. There was no marketing budget, no sales force, no customer success team. It was pure open-source passion, the kind of grassroots project that emerges when deeply talented people care intensely about a problem.
And yet, despite having none of the trappings of a commercial software company, Metasploit had achieved something that most commercial products never achieve: genuine love from its users. Security professionals did not just use Metasploit. They evangelized it. They contributed code to it. They wrote blog posts about it. They taught courses built around it. The quality was exceptional, the community was fiercely loyal, and the brand recognition among security practitioners was unmatched by any commercial product. In the security world, saying "I use Metasploit" was a credential in itself.
When Rapid7 announced the acquisition for an undisclosed sum, the hacker community's reaction was immediate and polarized. The skeptics saw it as a sellout, a beloved open-source project being consumed by a corporate entity that would inevitably prioritize profit over community. Forums lit up with criticism. "Another open-source project killed by corporate greed" was a common refrain. The optimists, and Moore himself, argued that Rapid7's backing would allow full-time development of the framework for the first time, accelerating innovation and ensuring Metasploit's long-term sustainability.
The optimists proved largely right. Moore joined Rapid7 as Chief Security Officer and later Chief Research Officer, maintaining his role as Metasploit's chief architect. Rapid7 committed to keeping the open-source Metasploit Framework freely available while building a commercial edition called Metasploit Pro on top of it. The commercial version added enterprise features like automation, comprehensive reporting, phishing simulation, and credential testing, capabilities that large organizations needed but that the open-source community had little incentive to build.
The strategic logic was elegant. Vulnerability scanning with Nexpose told you where your weaknesses were. Penetration testing with Metasploit proved whether those weaknesses could actually be exploited by an attacker. Together, they provided a complete picture of organizational risk that neither tool could deliver alone. A security team could run Nexpose to find ten thousand vulnerabilities, then run Metasploit to discover that only fifty of those ten thousand were actually exploitable in the current network configuration. That prioritization, from ten thousand theoretical problems to fifty real ones, was transformative for resource-constrained security teams. Rapid7 was no longer just a company that identified problems. It was a company that validated them, a crucial distinction in a market where security teams were drowning in alerts and struggling to prioritize what actually mattered.
But the acquisition's impact extended far beyond product synergy. Metasploit gave Rapid7 something that money cannot easily buy: authentic credibility with security practitioners. In cybersecurity, the opinions of the people who actually use the tools matter enormously. CISOs may sign the purchase orders, but the security engineers and analysts who deploy and operate the products are the ones who drive vendor selection. By becoming the stewards of the most beloved penetration testing tool in the world, Rapid7 earned a level of practitioner trust that competitors spent years and millions in marketing dollars trying to replicate.
The cultural integration was not without friction. Rapid7 was a commercial software company with sales targets, quarterly reviews, and corporate processes. The Metasploit community was anarchic, meritocratic, and allergic to anything that smelled like corporate interference. Navigating this tension required genuine restraint from Rapid7's leadership. They had to resist the temptation to over-commercialize the open-source project while still extracting business value from the acquisition. For the most part, they threaded the needle successfully, investing in the framework's development, growing the community, and building commercial revenue on top without killing the golden goose.
Metasploit also became a powerful talent magnet. Security researchers who might never have considered working for a vulnerability scanner company were drawn to Rapid7 because of the opportunity to work on or alongside Metasploit. This created a research-oriented culture within the company that distinguished it from competitors focused purely on enterprise sales. The "practitioner-first" DNA that Metasploit instilled would shape Rapid7's identity for the next decade and beyond, influencing everything from product design to marketing messaging to the way the company engaged with the broader security community.
For investors, the Metasploit acquisition offers a masterclass in the value of open-source communities as business assets. The acquisition cost was undisclosed but was almost certainly modest relative to the strategic value it delivered. It transformed Rapid7's brand, expanded its addressable market, created a competitive moat built on community loyalty, and established the company as a serious player in the offensive security space. The lesson is not that every open-source acquisition works. Many fail spectacularly. The lesson is that when a company genuinely commits to nurturing a community rather than extracting from it, the returns can be extraordinary. As the company prepared to enter the next decade, it carried both the commercial momentum of a growing scanner business and the cultural cachet of the security world's favorite hacking tool. What it did with that combination would define its future.
IV. Building the Platform: From Point Solution to Suite
Walk through the halls of any major cybersecurity conference in 2011 or 2012, RSA in San Francisco, Black Hat in Las Vegas, and you would see the telltale signs of a market in transition. The vendor booths were getting bigger. The marketing budgets were getting larger. And the pitch was changing. Every company was talking about "platforms" and "suites" and "integrated security." The days of buying individual point tools were ending, or so the marketing claimed.
The years between 2010 and 2015 represent Rapid7's transition from scrappy upstart to credible enterprise security company. The Metasploit acquisition had given the company a halo of practitioner credibility, but the underlying business still faced a fundamental strategic question that confronts every successful point-solution vendor: Do you stay focused and deep, or do you broaden into a platform?
The security vendor's dilemma is a particularly acute version of this tension. Enterprise security teams in the early 2010s were already suffering from what the industry calls "tool sprawl," the proliferation of dozens of specialized security products, each solving a narrow problem, none talking to each other, all generating alerts that overwhelmed understaffed teams. The average enterprise was running forty to sixty different security tools by some estimates. This created an opening for vendors who could consolidate multiple capabilities onto a single platform, reducing complexity and improving the overall security posture by correlating data across different domains.
Rapid7 began making small acquisitions to expand beyond its Nexpose and Metasploit core. In October 2012, the company acquired Mobilisafe, a Seattle-based mobile device risk management startup that was reportedly just days away from closing its Series B funding round when Rapid7 swooped in. Mobile devices were proliferating in the enterprise, and the ability to assess mobile risk complemented Rapid7's traditional network scanning capabilities. The deal was small but signaled an ambition to go beyond the company's original scope.
Behind the scenes, a more fundamental transformation was taking shape. Corey Thomas, who had joined Rapid7 in November 2008 as Senior Vice President of Marketing and Sales and played a central role in the Metasploit acquisition, was promoted to President and CEO in October 2012. Thomas brought a background that combined technical depth with business rigor. He held an engineering degree from Vanderbilt University and an MBA from Harvard Business School, and had spent time at Microsoft, where he led the worldwide availability strategy for SQL Server, and at Parallels, a virtualization company. He also had management consulting experience at Deloitte.
Thomas's leadership was transformative in a way that is not immediately obvious. He was one of the few Black CEOs in the cybersecurity industry, and he brought a combination of technical fluency and strategic ambition that was unusual for the role. Under his predecessor, Rapid7 had been primarily a product company, engineering-driven and sales-focused. Thomas reoriented the company around a platform vision, the idea that Rapid7's future lay not in individual products but in a unified data and analytics infrastructure that could power multiple security use cases. This vision would eventually become the Insight Platform, but in the early Thomas era, it manifested as a more disciplined approach to product development, go-to-market strategy, and operational execution. During this period, Rapid7 landed on the Inc. 500 list, with Thomas credited for driving roughly a nine-fold increase in revenue during his tenure leading sales and marketing.
The competitive landscape was intensifying. Tenable, founded in 2002, had grown into Rapid7's most direct competitor in vulnerability management, buoyed by the widespread adoption of its Nessus scanner, arguably the most deployed vulnerability assessment tool in history. Nessus had become the de facto standard for vulnerability assessment in much the same way that Microsoft Office had become the default for productivity software. It was not always the best tool for every situation, but it was the one that almost everyone knew, almost everyone had used, and almost every training program taught. Competing against that level of incumbency is enormously difficult.
Qualys, which had pioneered the cloud-delivered vulnerability scanning model years before the rest of the industry caught on, was pushing aggressively on its Software-as-a-Service platform. And a host of newer entrants were eyeing the market from adjacent categories. The days when Rapid7 could grow simply by being a better scanner were ending. The company needed scale, and to get scale, it needed the public markets.
Rapid7 went public on July 16, 2015, listing on the NASDAQ under the ticker RPD. The IPO priced at sixteen dollars per share, with the company selling approximately 6.45 million shares and raising about one hundred and three million dollars in gross proceeds. The initial valuation at the IPO price was roughly six hundred and five million dollars, but the market's enthusiasm pushed the stock to an intraday high of twenty-seven dollars and forty-five cents on its first day of trading, briefly implying a market capitalization above one billion dollars. Morgan Stanley and Barclays served as joint book-running managers.
At the time, Rapid7 reported trailing annual revenue of approximately one hundred and ten million dollars, growing at over forty percent year over year. The growth was impressive, but the company was not profitable, operating in the classic enterprise SaaS mode of investing aggressively in sales, marketing, and product development to capture market share. The IPO gave Rapid7 the capital and currency it needed for the next phase of its evolution, but it also introduced the relentless pressure of public market expectations. Quarterly earnings calls, analyst estimates, and stock price volatility would now shape every strategic decision, creating a tension between long-term platform building and short-term financial performance that would define the next several years of the company's life.
V. The Cloud Inflection Point and Platform Rebuild
If you had to pick a single moment when the ground began shifting beneath Rapid7's feet, it would be sometime around 2014 or 2015, when the cloud transformation of enterprise IT crossed from theoretical possibility to operational reality. Amazon Web Services, which had been growing rapidly since the late 2000s, was now generating tens of billions in revenue. Microsoft Azure was scaling aggressively. Google Cloud Platform was investing heavily. And enterprise IT departments, initially skeptical about putting sensitive workloads in somebody else's data center, were migrating at an accelerating pace.
For a vulnerability management company like Rapid7, this shift was nothing short of existential. The entire premise of traditional vulnerability scanning rested on a simple assumption: you have a network with a defined perimeter, you deploy scanners inside that perimeter, and they systematically probe your assets to find weaknesses. It is like hiring a security guard for a building. The guard knows the building, walks the floors, checks the locks. Simple and effective.
But cloud computing dissolved the building. Imagine your company no longer operates in a single physical location. Instead, your employees work in hundreds of temporary offices that appear and disappear throughout the day. Your servers are not servers anymore; they are ephemeral computing instances that spin up to handle a burst of traffic and vanish minutes later. Your applications are not monolithic programs running on known hardware; they are collections of microservices, dozens or hundreds of tiny interconnected programs running in containers, essentially lightweight virtual machines that can be created, destroyed, and recreated in seconds.
How do you scan something that might not exist five minutes from now? How do you maintain a vulnerability inventory when the inventory itself is in constant flux? The traditional scanning approach, running periodic assessments against a known set of assets, was becoming inadequate for a world where the assets themselves were ephemeral. Applications were being deployed through continuous integration and continuous delivery pipelines, known as CI/CD, that pushed new code to production dozens or hundreds of times per day. Security had to move at developer speed or risk being bypassed entirely.
Simultaneously, a new generation of cloud-native security startups was emerging, companies built from scratch for the cloud era, carrying no legacy technology debt, and designing their products around the architectural patterns that enterprises were adopting. These startups had a fundamental advantage: they did not need to manage a transition. They did not need to maintain on-premises products for existing customers while simultaneously building cloud-native alternatives. They could focus exclusively on the future.
This dynamic is worth dwelling on because it recurs constantly in enterprise software. The startup advantage is not smarter engineers or better ideas. It is the absence of an installed base that must be maintained. Every hour a Rapid7 engineer spent keeping Nexpose working for an on-premises customer was an hour not spent building cloud-native capabilities. Every dollar of Nexpose revenue that needed to be protected was a dollar of organizational attention diverted from the future. Clayton Christensen described this exact phenomenon in "The Innovator's Dilemma," and Rapid7 was living it in real time, knowing the answer but finding it agonizingly difficult to act on.
For Rapid7, the challenge was acute. Nexpose, the product that had been the company's bread and butter for over a decade, was an on-premises tool. It generated significant revenue from existing customers who were not ready to move to the cloud. Abandoning it would destroy current revenue. But failing to build a cloud-native alternative would cede the future to competitors who had no legacy to protect. This is the classic innovator's dilemma, described by Clayton Christensen and lived in real time by technology companies across every generation.
Corey Thomas, now firmly established as CEO, made the call to invest aggressively in a cloud-native platform. The result was the Insight Platform, a unified cloud-based data and analytics backbone designed to power multiple security products. The technical architecture was ambitious: a scalable data lake that could ingest security telemetry from across an organization's environment, network traffic, endpoint data, cloud configurations, application logs, and deliver analytics and insights through a suite of purpose-built products.
The product launches came in waves. InsightIDR, a cloud-native incident detection and response tool that essentially positioned Rapid7 as a challenger to legacy SIEM vendors like Splunk, launched in February 2016. InsightVM, the cloud-powered successor to Nexpose for vulnerability management, and InsightAppSec, a dynamic application security testing product, followed in April 2017. That same year, Rapid7 acquired Komand, a security orchestration and automation company, which became the foundation for InsightConnect, the platform's automation and workflow engine. InsightConnect reached general availability in October 2018.
Each of these products represented not just a new SKU but a fundamental replatforming effort. The engineering teams had to rebuild capabilities that had been refined over years in on-premises architectures, this time for cloud-native deployment. The data models were different. The performance requirements were different. The user experience expectations were different. And all of this had to happen while continuing to support and sell the legacy Nexpose product to customers who were not yet ready to transition.
The financial impact was painful. The transition from perpetual licenses to subscription-based SaaS revenue created the classic "trough of disillusionment" in the financial statements. Revenue growth slowed. Margins compressed as the company invested heavily in cloud infrastructure and engineering. The stock, which had traded above thirty dollars at its post-IPO highs, spent much of 2016 and 2017 well below twenty dollars. Analysts and investors were skeptical. "Another security vendor claiming cloud transformation" was the sentiment, and Rapid7 had to prove that its platform bet was not just a marketing exercise.
The acquisition of tCell in October 2018 for approximately fourteen million dollars added runtime application self-protection capabilities to the portfolio, further expanding the platform's scope. But the fundamental challenge remained: could Rapid7 execute the transition fast enough to remain relevant before cloud-native competitors and platform behemoths captured the market? The answer was still unclear as the company entered the product explosion era, but the foundation, for better or worse, was being laid. The Insight Platform was real. The products were shipping. And for the first time, Rapid7 had a coherent vision of what it wanted to be when it grew up: not a vulnerability scanner company, but a security analytics platform that could serve as the operating system for enterprise security teams. Whether the market would give it enough time to realize that vision was another question entirely.
VI. The Product Explosion Era
Between 2017 and 2021, Rapid7 underwent a transformation that was as impressive in ambition as it was daunting in execution. The company went from being primarily known for two products, Nexpose and Metasploit, to operating a family of six or more cloud-based offerings under the Insight brand, each targeting a distinct slice of the enterprise security market. It was the corporate equivalent of a single-instrument musician deciding to form an entire orchestra.
The pivot that mattered most was the bet on SIEM, Security Information and Event Management. For the uninitiated, SIEM is essentially the central nervous system of a security operations center. It collects logs and alerts from every device, application, and security tool in an organization, correlates them to identify patterns that might indicate an attack, and presents them to human analysts for investigation. Think of it as air traffic control for cybersecurity: hundreds of signals coming in simultaneously, and the SIEM's job is to identify which ones represent genuine threats versus normal activity.
InsightIDR was not just another product in the Rapid7 portfolio. It was the growth engine that would define the company's financial trajectory for the next several years. Traditional SIEM had been dominated by Splunk, a company that had built a massive business on the ability to ingest, index, and search vast quantities of machine data. But Splunk was notoriously expensive, with licensing costs that scaled with data volume, meaning that as organizations generated more data, their Splunk bills grew faster than their budgets. Splunk was also complex to deploy and increasingly seen as a solution designed for a prior generation of IT architecture. InsightIDR offered a cloud-native alternative that was easier to deploy, cheaper to operate, and purpose-built for security use cases rather than general-purpose log management.
The pitch to customers was compelling: instead of buying separate tools for vulnerability management, incident detection, and security automation, why not consolidate onto a single platform? The Insight suite products shared a common data layer, which meant that insights from one product could inform another. Vulnerabilities discovered by InsightVM could be correlated with threat detections from InsightIDR, and response actions could be automated through InsightConnect. This integrated approach was genuinely differentiated in a market where most security vendors sold isolated point solutions that left customers to figure out the integration themselves.
The land-and-expand sales motion worked beautifully during this period. A customer who initially bought InsightVM for vulnerability management could be upsold to InsightIDR for threat detection, then to InsightConnect for automation, and so on. Each additional product deepened the customer relationship, increased switching costs, and expanded annual recurring revenue per account. This was the flywheel that every platform company dreams about, and for a few years, Rapid7 was spinning it effectively.
To understand why this mattered so much financially, consider the math. Acquiring a new enterprise customer in cybersecurity is expensive. It requires multiple sales calls, proof-of-concept deployments, security reviews, procurement cycles, and often months of effort from an account executive, a solutions engineer, and a sales development representative. If all of that effort results in a single product sale generating, say, one hundred thousand dollars in annual recurring revenue, the economics are marginal at best. But if that same customer can be expanded to three or four products over the following two to three years, the annual recurring revenue per account triples or quadruples while the incremental acquisition cost is minimal, since you already have the relationship, the deployed infrastructure, and the organizational trust. This is the fundamental economic logic of the platform strategy, and it explains why Rapid7 pursued it so aggressively.
The acquisition strategy accelerated to keep pace with expanding ambitions. In April 2020, Rapid7 acquired DivvyCloud for one hundred and forty-five million dollars, adding cloud security posture management to its portfolio. DivvyCloud became the foundation for InsightCloudSec, a product designed to help organizations manage security and compliance across multi-cloud environments. This was a direct response to the market's rapid shift toward what Gartner would later call Cloud-Native Application Protection Platforms, or CNAPP, a convergence of workload protection, posture management, and cloud infrastructure security.
In February 2021, the company acquired Alcide, a Tel Aviv-based Kubernetes security startup, for approximately fifty million dollars, adding container and Kubernetes runtime protection to its cloud security capabilities. And then came the big one: in the second half of 2021, Rapid7 completed the acquisition of IntSights, a New York-based threat intelligence company, for three hundred and thirty-five million dollars. This was the largest acquisition in Rapid7's history and represented a major bet on external threat intelligence, the ability to monitor the dark web, underground forums, and other external sources for threats targeting specific organizations.
The sales transformation during this period was equally significant. Rapid7 had to evolve from a company that sold individual products to security practitioners into one that sold a multi-product platform to enterprise executives. This required building out a field sales organization with account executives who could navigate complex procurement processes, establishing channel partnerships with value-added resellers and managed security service providers, and investing in customer success teams whose job was to ensure existing customers adopted additional products. The land-and-expand playbook became the company's primary growth engine: acquire a customer with one product, demonstrate value, and then cross-sell the rest of the portfolio.
The financial results during this era were strong by most measures. Revenue grew from approximately two hundred million dollars in 2017 to five hundred and thirty-five million in 2021, a compound annual growth rate of roughly twenty-eight percent. The company reached six hundred and eighty-five million in 2022, meaning it more than tripled revenue in five years. The stock responded accordingly, rising from the teens to an all-time high of about one hundred and forty dollars in November 2021. For a brief, intoxicating moment, Rapid7 looked like it had successfully executed the platform pivot. The multi-product strategy was working. Revenue was growing. The stock was soaring. And the company had positioned itself as a comprehensive security analytics platform rather than a mere vulnerability scanner.
But beneath the surface, warning signs were emerging that would become impossible to ignore within a year. The "too many products" problem was becoming real. In cybersecurity, there is a well-known phenomenon called "alert fatigue," where security analysts become overwhelmed by the sheer volume of alerts from their tools and start ignoring them. Rapid7 was experiencing the corporate equivalent. Each acquisition brought its own technology stack, its own engineering team, its own customer base, and its own integration challenges. Making all of these pieces work together seamlessly on the Insight Platform was a Herculean engineering task that consumed enormous resources. Some customers complained that individual products lacked the depth of best-of-breed alternatives. Others found the integration between products less smooth than the marketing promised. And the sales organization, now tasked with selling a complex portfolio of products rather than one or two straightforward solutions, was struggling with the complexity.
The narrative had shifted from "vulnerability management company" to "security analytics platform," but narrative alone does not build a moat. As the company prepared to enter 2022, it carried both the momentum of impressive growth and the weight of an increasingly sprawling product portfolio. The market was about to test whether that portfolio was a strength or a liability.
VII. The 2020s: Market Turbulence and Identity Crisis
There is a particular cruelty to the way public markets punish growth companies that stumble. When everything is working, when revenue is growing at thirty percent and the stock is climbing, the market gives you the benefit of the doubt on profitability, integration challenges, and competitive threats. When the music stops, all of those deferred concerns arrive at once, and the reckoning can be savage.
For Rapid7, the music stopped in 2022. Consider the magnitude of the destruction. A share of RPD bought at the November 2021 peak for one hundred and forty dollars was worth less than ten dollars by early 2026, a decline of over ninety-five percent. An investor who bought at the IPO price of sixteen dollars and held through the entire journey, surviving the early struggles, celebrating the cloud pivot, enduring the pandemic volatility, and riding the 2021 euphoria, would have seen their investment lose more than half its value over a decade. That is not a story of a failing business. It is a story of a market that priced in a future that did not materialize.
The collapse was driven by a confluence of factors, some macroeconomic, some competitive, and some self-inflicted.
The macroeconomic headwinds were brutal and indiscriminate. The Federal Reserve's aggressive interest rate hikes beginning in early 2022, the fastest tightening cycle in four decades, triggered a wholesale repricing of growth technology stocks. Companies valued on the promise of future earnings saw their multiples compress dramatically as the discount rate applied to those future earnings increased. Rapid7, which had never been consistently profitable and was valued primarily on revenue growth, was caught directly in the crosshairs. SaaS companies across the board saw their valuations cut in half or worse, but Rapid7 suffered more than most because the growth story was simultaneously weakening.
Revenue growth, which had been running at twenty-eight percent in 2022, decelerated to roughly thirteen percent in 2023 and then to just under nine percent in 2024. To put that trajectory in context: in five years, Rapid7 went from growing at nearly thirty percent, which is the kind of growth rate that justifies premium SaaS valuations, to growing at single digits, which is the kind of growth rate that gets a software company's stock treated like a declining industrial business. The slowdown reflected multiple pressures. Enterprise security budgets were tightening as the broader economy softened. Buyers were pushing back on security tool proliferation, demanding fewer vendors and more consolidated solutions. And competition was intensifying from every direction. CrowdStrike, with its Falcon platform, was expanding from endpoint security into adjacent categories that overlapped with Rapid7's products. Palo Alto Networks was executing an aggressive platformization strategy, acquiring companies and bundling capabilities in ways that made it difficult for mid-tier vendors to compete. And Wiz, a privately held cloud security startup reportedly valued at over twelve billion dollars after turning down a reported twenty-three billion dollar acquisition offer from Google, was rapidly capturing the cloud security posture management market that Rapid7 had entered with the DivvyCloud acquisition.
In early 2023, Rapid7 hired Goldman Sachs and JPMorgan to explore strategic options, including a potential sale. Reports surfaced that Thoma Bravo, the private equity firm that has become the most prolific acquirer of cybersecurity companies, made an offer. But the parties were reportedly too far apart on price, and no deal materialized. Thoma Bravo instead turned its attention to Darktrace, the UK-based cybersecurity company, which it acquired for approximately five point three billion dollars in a deal announced in April 2024 and completed in October 2024.
The failed take-private process was a turning point. It confirmed that the market saw Rapid7 as a company in need of restructuring, but the price gap suggested that even private equity buyers were not willing to pay a premium for a business with decelerating growth and an overstretched product portfolio. For public market investors, the signal was discouraging.
In August 2023, Rapid7 announced an eighteen percent workforce reduction, cutting approximately four hundred and seventy employees out of a workforce of roughly twenty-six hundred. Office closures followed, along with a one-time restructuring charge of about twenty-seven million dollars. The cuts were swift and deep, affecting engineering, sales, and administrative functions across the organization. For a company that had spent years building out teams to support its expanding product portfolio, the layoffs represented an acknowledgment that the growth-at-all-costs era was over.
The restructuring had an immediate and dramatic effect on the financial profile: free cash flow guidance was raised from eighty million to one hundred and sixty million dollars, essentially doubling the cash generation of the business through cost reduction alone. This raised an uncomfortable question: had the company been systematically overspending during the growth years, or was this the kind of painful but necessary right-sizing that every maturing software company must eventually undertake? The answer was probably both.
Then came the activist investors. Jana Partners, a well-known activist hedge fund with a history of pushing technology companies toward sales or restructurings, disclosed a significant stake in Rapid7 beginning in mid-2024. The initial position was approximately five point eight percent and grew steadily to over ten percent by August 2025, signaling serious intent.
Jana's playbook is well-established in the technology sector. The firm identifies companies that it believes are undervalued relative to their strategic assets, takes a significant stake, and then publicly or privately pressures management and the board to explore "strategic alternatives," which typically means a sale to a private equity firm or a larger strategic acquirer. Jana publicly pressured Rapid7 to explore exactly this path, arguing that the company's value was not being reflected in its stock price and that a private equity buyer could unlock value through operational improvements and strategic focus.
In October 2024, Reuters reported that Rapid7 was again fielding buyout interest, with the company valued at approximately two point five billion dollars, a fraction of its peak market capitalization but still a meaningful premium to where the stock was trading at the time.
The company has not been sold. In March 2025, Rapid7 entered a cooperation agreement with Jana Partners, adding three new directors to its board, including a Jana representative. This compromise effectively gave the activist a seat at the table without forcing an immediate sale, buying time for the company to demonstrate whether its turnaround strategy could work under current ownership. It is worth noting the regulatory and legal overlay here: the cooperation agreement typically includes standstill provisions that limit the activist's ability to launch a proxy fight for a defined period, in exchange for board representation. These agreements are structured to create a window of collaboration rather than confrontation, though the underlying tension between activist impatience and management's longer-term vision remains ever-present.
For investors parsing the Rapid7 story, the 2022-2025 period crystallizes a uncomfortable truth about mid-tier enterprise software companies. When you are big enough to be publicly traded but not big enough to be a platform leader, you exist in a dangerous middle ground. You are too large and established for venture-backed agility, but too small to match the distribution and bundling power of the giants. The private equity interest validates that the business has real value, with nearly eight hundred and sixty million in revenue and one hundred and fifty-four million in free cash flow in 2024. But the gap between the activist's vision of what the company could be worth and its actual trading price tells you everything about the market's skepticism regarding the company's ability to reignite growth.
VIII. The Vulnerability Management Market Evolution
To understand where Rapid7 stands today, you need to understand how the category it helped create has transformed beyond recognition. Vulnerability management in 2000, when Rapid7 was founded, was a straightforward proposition: scan your network periodically, produce a list of vulnerabilities ranked by severity, and give that list to your IT team to fix. The cadence was typically quarterly. The scope was limited to assets you knew about. And the output was a static report that was often outdated by the time anyone acted on it.
To put the scale of the vulnerability problem in context, the Common Vulnerabilities and Exposures database, the industry standard registry of known security flaws, added over twenty-eight thousand new entries in 2023 alone. That is roughly seventy-seven new vulnerabilities discovered every single day. A decade earlier, the annual total was closer to five thousand. The explosion reflects both the increasing complexity of software and the growing sophistication of the security research community in finding flaws. For organizations trying to stay ahead of attackers, the challenge is not finding vulnerabilities. It is managing the overwhelming volume and determining which ones actually pose a risk to their specific environment.
The first evolution was from periodic to continuous. As networks grew more complex and new vulnerabilities were discovered at an accelerating pace, the quarterly scan became insufficient. Companies like Qualys pioneered the cloud-delivered model that allowed for more frequent, even continuous, scanning. Rapid7's InsightVM pushed in the same direction, offering live dashboards and real-time visibility into vulnerability posture rather than point-in-time reports.
The second evolution was from vulnerability counting to risk prioritization. The sheer volume of vulnerabilities in any large enterprise network is staggering, tens of thousands or even hundreds of thousands of individual findings. Early vulnerability management tools treated them all more or less equally, producing reports so long that security teams could not meaningfully act on them. The industry responded by developing risk-based approaches that used threat intelligence, exploit availability, and asset criticality to prioritize the vulnerabilities that actually mattered. Rapid7's risk scoring, Tenable's Vulnerability Priority Rating, and Qualys's TruRisk all represent variations on this theme.
The third and most disruptive evolution has been the fragmentation and reconvergence of the market itself. This is one of the most confusing aspects of the cybersecurity industry for outside observers, and it is worth unpacking carefully. What used to be a single category called vulnerability management has splintered into a constellation of overlapping segments, each with its own acronym, its own Gartner Magic Quadrant, and its own set of vendors claiming to be the market leader. Cloud Security Posture Management, or CSPM, focuses on identifying misconfigurations in cloud infrastructure. Cloud-Native Application Protection Platforms, or CNAPP, attempt to unify workload protection, posture management, and cloud security into a single offering. Attack Surface Management, or ASM, extends visibility beyond the traditional network perimeter to include external-facing assets, third-party risks, and shadow IT. And Exposure Management, a term Gartner has promoted, attempts to provide a holistic view of organizational risk that encompasses all of these categories.
Each of these new categories represents both a threat and an opportunity for traditional vulnerability management vendors. The threat is obvious: budget dollars that used to flow to VM tools are now being split across CSPM, CNAPP, ASM, and other categories. But the opportunity is that vendors who can credibly deliver across multiple categories have a chance to consolidate spending and become indispensable platform partners.
The competitive landscape has shifted dramatically. In the traditional VM space, Tenable remains the most direct competitor, with its Nessus scanner installed in more organizations than any other vulnerability assessment tool and its Tenable One platform providing exposure management capabilities. Qualys continues to compete effectively with a cloud-native approach and strong compliance automation. But the real threat comes from outside the traditional VM category. Wiz has captured enormous market share in cloud security with an agentless, graph-based approach that resonates with cloud-native organizations. Palo Alto Networks has assembled a formidable cloud security portfolio through acquisitions and organic development. CrowdStrike's Falcon platform, originally focused on endpoint detection, now extends into vulnerability management, cloud security, and identity protection. And Microsoft, with its Defender suite and Sentinel SIEM, is bundling security capabilities into its enterprise licensing in ways that are difficult for standalone vendors to match.
Rapid7's positioning challenge is that it is caught between these forces. It is not the leader in traditional vulnerability management, where Tenable has stronger market share and Nessus remains the most widely deployed scanner in the world. It is not the leader in cloud-native security, where Wiz has captured the imagination of cloud-first organizations with its agentless approach and graph-based visualization of cloud risk. It is not the leader in platform security, where CrowdStrike and Palo Alto Networks have stronger brands, deeper product portfolios, and significantly larger R&D budgets. CrowdStrike alone spends more on research and development annually than Rapid7 generates in total revenue. And Rapid7 cannot match Microsoft's ability to bundle security into existing enterprise agreements at marginal cost, a strategy that effectively makes Microsoft's security offerings "free" from the buyer's perspective, since they are included in licenses the customer was already going to purchase. The company's response has been to lean into managed services, specifically Managed Detection and Response, as a differentiator that combines technology with human expertise in a way that pure product vendors cannot easily replicate. Whether this is a sustainable strategy or a retreat into a lower-growth niche is one of the central questions facing the company and its investors.
IX. Today and the Path Forward
In early 2026, Rapid7 presents a study in contradictions. The company generates meaningful revenue, nearly eight hundred and sixty million dollars in 2025, and has demonstrated the ability to produce substantial free cash flow, roughly one hundred and fifty-four million dollars in 2024. It has a customer base that spans thousands of organizations worldwide. Its products cover a wide swath of the security landscape. And its brand, bolstered by the ongoing stewardship of Metasploit, still carries weight with security practitioners.
But the growth story has stalled. Revenue grew less than two percent in 2025, and the company's guidance for 2026 calls for revenue between eight hundred and thirty-five million and eight hundred and forty-three million dollars, essentially flat to slightly declining. The stock, trading near six dollars in early 2026, reflects a market capitalization of roughly four hundred and fifty-seven million dollars, a fraction of the company's peak valuation. Annual recurring revenue sat at eight hundred and forty million dollars at the end of 2025, showing minimal expansion.
Under the pressure of activist investors and competitive forces, Rapid7 has been rationalizing its product portfolio. The sprawling Insight family is being focused around core strengths: InsightVM for vulnerability management, InsightIDR for detection and response, and InsightCloudSec for cloud security. Peripheral products and underperforming acquisitions are being de-emphasized or integrated more tightly into the core platform. The goal is to move from "many products, loosely joined" to a more cohesive platform experience.
In March 2023, the company acquired Minerva Labs, an Israeli ransomware prevention firm, for approximately thirty-eight million dollars. In July 2024, it added Noetic Cyber, a cyber asset attack surface management company, for roughly fifty-one million dollars. These smaller, targeted acquisitions reflect a more disciplined approach to M&A than the larger, more ambitious deals of the 2020-2021 era. They fill specific capability gaps rather than attempting to enter entirely new markets.
The most significant strategic bet is on Managed Detection and Response, a service in which Rapid7 provides twenty-four-seven human-led threat detection, investigation, and response on behalf of customers. MDR addresses a fundamental market reality: most organizations do not have the staff, skills, or resources to operate a security operations center on their own. By combining its technology platform with skilled human analysts, Rapid7 can deliver outcomes rather than tools, a proposition that resonates particularly well with mid-market organizations that lack dedicated security operations teams.
In January 2025, the company launched MDR for Microsoft, extending its managed services capabilities to organizations that have standardized on Microsoft's security ecosystem, including Defender and Sentinel. This was a pragmatic acknowledgment that Microsoft's security suite has become the default choice for many enterprises, and rather than fighting that tide, Rapid7 can add value by providing the operational expertise that Microsoft's tools alone do not deliver.
The artificial intelligence narrative is impossible to ignore. Like every technology company in 2025 and 2026, Rapid7 has leaned into AI as a strategic differentiator. The company has been investing in what it calls AI-enabled security operations and agentic AI workflows within its MDR offering, essentially using AI to automate routine investigation tasks, accelerate threat analysis, and augment the capabilities of human analysts. Whether this represents a genuine competitive advantage or table-stakes capability that every vendor will offer remains to be seen.
Leadership has evolved under the pressure. Corey Thomas remains CEO, but the board composition has changed significantly, particularly with the addition of directors aligned with Jana Partners following the March 2025 cooperation agreement. The board's strategic direction now reflects a tension between the activists' desire for a sale or restructuring and management's belief that the company can execute a turnaround as an independent public entity. Strategic partnerships with companies like ARMO for runtime cloud security and HITRUST for compliance automation suggest a strategy of building ecosystem relationships rather than trying to own every capability internally.
The integration challenge remains the company's most significant operational hurdle. Acquisitions spanning Metasploit, DivvyCloud, IntSights, Alcide, Minerva Labs, and Noetic Cyber have brought diverse technologies into the portfolio, each with its own architecture, data models, and customer base. Making these disparate components work together as a coherent platform is an engineering challenge that has consumed years of effort and significant resources. Progress has been made, but the gap between the marketing promise of a unified platform and the operational reality of managing multiple technology stacks remains a persistent source of customer friction and internal complexity.
X. Business Model and Go-to-Market Evolution
Rapid7's business model evolution mirrors the broader transformation of enterprise software from perpetual licenses to subscription SaaS, but with the additional complexity that comes from selling security products to risk-averse buyers in a crowded market.
In its earliest years, the company sold Nexpose and Metasploit Pro through perpetual licenses, a model where customers paid a large upfront fee for the right to use the software indefinitely, plus an annual maintenance fee for updates and support. This model had predictable economics: large initial deals that front-loaded revenue recognition, followed by a stream of maintenance revenue that was relatively stable but did not grow rapidly.
The transition to subscription-based SaaS, which accelerated with the launch of the Insight Platform, fundamentally changed these economics. Under the subscription model, revenue is recognized ratably over the contract term rather than upfront, which means that even if a customer signs a larger total deal, the revenue appears more gradually in the financial statements. This creates the infamous "SaaS transition trough" where reported revenue growth temporarily slows even as the underlying business health improves. For Rapid7, this transition played out over several years, and the financial complexity it created made it difficult for investors to assess the company's true trajectory.
The go-to-market motion has evolved through three distinct phases. In the early days, Rapid7 sold primarily to security practitioners in a bottom-up motion. Individual security engineers or small security teams would discover Nexpose or Metasploit, evaluate the products, and champion them internally. The sales cycles were relatively short, deal sizes were modest, and the relationship was deeply technical. This practitioner-first approach, reinforced by the Metasploit community, gave Rapid7 an authentic grassroots presence that larger competitors envied.
As the company grew and the product portfolio expanded, the go-to-market shifted toward enterprise sales teams and channel partnerships. Selling a multi-product platform to large organizations requires a fundamentally different sales motion than selling a single product to security teams. Account executives need to understand the full portfolio, articulate the value of the platform rather than individual tools, and navigate complex procurement processes involving CISOs, CIOs, and procurement departments. Rapid7 built out an enterprise sales force, established channel partnerships with major distributors and managed security service providers, and invested in customer success teams to drive retention and expansion.
The current era adds managed services as a significant revenue driver and a strategic differentiator. MDR is not sold the same way as software products. It requires a consultative sales process, detailed scoping of the customer's environment, and a clear articulation of the service-level commitments and operational model. The economics are different too: managed services typically carry lower gross margins than pure software sales because they require ongoing human labor, but they generate highly predictable recurring revenue and create deep customer relationships that are difficult for competitors to displace.
Professional services, training, and certification programs provide additional revenue streams and serve the dual purpose of generating margin and deepening customer engagement. Rapid7 offers security training through its open-source community activities and commercial training programs, creating a pipeline of practitioners who are trained on Rapid7 tools and predisposed to recommend them in their organizations.
One important nuance of the SaaS transition that is often overlooked by investors unfamiliar with the model: the shift from perpetual licenses to subscriptions does not just change revenue recognition. It fundamentally alters the cash flow dynamics of the business. Under perpetual licensing, customers paid large sums upfront, which meant cash came in before the company delivered the full value. Under subscription models, cash arrives ratably, but the company incurs most of the costs of acquiring and onboarding the customer upfront. This creates a period where customer acquisition costs front-load expenses while revenue trickles in over time. For a company transitioning its entire base from one model to the other, the financial statements can look significantly worse even if the underlying business is getting healthier. Understanding this dynamic is essential for evaluating Rapid7's financial history during the 2015-2019 transition period.
The unit economics of security companies deserve special attention because they differ structurally from other software categories. Security products are not "nice to have" purchases that get cut in downturns; they are often compliance requirements that must be maintained regardless of economic conditions. This creates a base level of demand stability that few other software categories enjoy. However, security buying decisions are also characterized by extreme vendor fatigue. CISOs are bombarded with pitches from hundreds of security vendors, each claiming to solve a critical problem, and the resulting skepticism makes customer acquisition costs in security structurally higher than in many other software categories. The combination of high retention and high acquisition costs means that customer lifetime value in security tends to be very high, but only for vendors who can retain and expand their customer base. Net revenue retention, the measure of how much existing customers spend year over year, is arguably the single most important metric for understanding Rapid7's business health.
XI. Playbook: Business and Investing Lessons
The Rapid7 story, spanning more than twenty-five years from founding to its current moment of reckoning, offers several lessons that extend well beyond cybersecurity.
The first and most fundamental lesson is about the innovator's dilemma in enterprise software. Rapid7 faced the classic Christensen trap: its legacy on-premises products were generating real revenue from real customers who were not ready to move to the cloud. The temptation to protect that revenue by slowing the cloud transition was enormous. To the company's credit, it did not succumb to that temptation. It invested aggressively in the Insight Platform and pushed customers toward cloud-native products even when that meant cannibalizing its own installed base. But executing this transition while simultaneously maintaining the legacy business consumed enormous resources and management attention, and the dual-track approach created complexity in the product portfolio, the engineering organization, and the sales motion that the company is still working to resolve.
The second lesson concerns open source as an enterprise moat. The Metasploit acquisition remains the most instructive example in the Rapid7 playbook. By acquiring and nurturing a beloved open-source project, Rapid7 gained brand credibility, community engagement, a talent pipeline, and a product development engine that would have taken years and hundreds of millions of dollars to build from scratch. The lesson is not simply that open-source acquisitions work, many do not, but that the acquirer's commitment to the community determines the outcome. Rapid7 maintained the open-source Metasploit Framework, invested in its development, and built commercial products on top of it rather than replacing it. This approach preserved community trust while extracting business value. Companies considering open-source acquisitions today should study the Metasploit integration closely.
The third lesson is about the strategic pendulum between platform and point solution. Rapid7 started as a point solution in vulnerability scanning, expanded into a platform with the Insight suite, and is now potentially swinging back toward focused excellence in a few core areas.
This pendulum swings regularly in enterprise software. In the 1990s, the trend was toward best-of-breed point solutions. In the 2000s, it shifted toward integrated suites, exemplified by the rise of ERP platforms like SAP and Oracle. In the 2010s, the cloud era brought a new wave of point solutions, each disrupting a specific function. And in the 2020s, the pendulum is swinging back toward platforms again, driven by buyer fatigue and the desire to reduce tool sprawl. The lesson is that the "right" answer changes over time and depends on market conditions, competitive dynamics, and the company's execution capabilities. During the 2017-2021 period, the platform narrative drove growth and stock price appreciation. In the post-2022 period, the breadth of the portfolio became a liability, spreading resources too thin and making it difficult to compete with focused competitors in any single category.
The fourth lesson involves mergers and acquisitions as product development. Rapid7 used M&A aggressively to fill portfolio gaps: DivvyCloud for cloud security posture, IntSights for threat intelligence, Alcide for Kubernetes security, Minerva Labs for ransomware prevention, Noetic Cyber for attack surface management.
Some of these acquisitions created genuine value. DivvyCloud, for instance, gave Rapid7 a meaningful presence in the cloud security posture market that would have taken years to build organically. Others added complexity without proportionate returns. The pattern suggests that M&A works best when the acquired technology can be deeply integrated into an existing platform and worst when it remains a semi-independent product that adds to the portfolio's sprawl without improving the overall platform experience.
The broader lesson for investors evaluating M&A-driven growth strategies: count the number of acquisitions, and then count the number of those acquisitions whose products are genuinely integrated into the core platform versus those that remain standalone. The ratio tells you whether the company is building a platform or collecting products.
The fifth lesson concerns the importance of practitioner credibility in cybersecurity. Unlike many enterprise software categories where the buyer (the executive who signs the check) and the user (the person who operates the tool) are different people with different priorities, cybersecurity has a uniquely powerful practitioner influence dynamic. Security engineers, analysts, and researchers have outsized influence on vendor selection because the consequences of choosing the wrong tool are immediate and severe. Rapid7's investment in practitioner credibility through Metasploit, community engagement, and research publications paid dividends for years. The lesson for other security vendors is that marketing to executives is necessary but not sufficient; you must also earn the respect of the people who will actually use your products.
The sixth lesson addresses public versus private ownership for growth companies in transition. The exploration of a sale to private equity, the activist pressure from Jana Partners, and the ongoing debate about Rapid7's future all highlight a structural tension in public markets.
Companies undergoing fundamental transitions need time to restructure, invest, and execute without the quarterly scrutiny of earnings calls and stock price movements. Private equity ownership can provide that time, but at the cost of loading the company with debt and optimizing for financial engineering over product innovation. The cybersecurity industry is littered with examples of both outcomes: Thoma Bravo's acquisition of SolarWinds allowed operational improvements but was followed by the devastating supply chain attack that damaged the brand. Its acquisitions of companies like Proofpoint and ForgeRock have had mixed results.
The fact that Rapid7 remains public while under activist pressure creates a hybrid dynamic that is neither fully public-market-driven nor fully PE-driven, and the outcome of this experiment will be instructive for other mid-tier software companies facing similar pressures.
The final lesson is about why cybersecurity is resistant to winner-take-all dynamics. Unlike cloud computing (dominated by three providers) or search (dominated by one), cybersecurity remains a fragmented market with hundreds of vendors across dozens of categories. This is because the threat landscape is constantly evolving, creating niches for specialized solutions; because enterprises are reluctant to entrust all security to a single vendor, since a single point of failure in security is existentially dangerous; and because the consequences of failure are so severe that defense-in-depth, using multiple overlapping tools, remains a fundamental security principle.
This structural fragmentation means that companies like Rapid7 can survive and even thrive in niches, but it also means that the dream of becoming the "one platform to rule them all" is extraordinarily difficult to realize. The cybersecurity market will likely always look more like the restaurant industry, many competitors serving different segments with different specialties, than the search engine market, one dominant player capturing the vast majority of value. That is both the comfort and the challenge for Rapid7 and its investors.
XII. Strategic Analysis: Competitive Positioning and Market Forces
Understanding Rapid7's competitive position requires examining both the structural forces shaping the cybersecurity market and the specific competitive advantages, or lack thereof, that the company brings to the fight.
The threat of new entrants in cybersecurity is medium to high. Cloud-native architectures have dramatically lowered the capital requirements for launching a security startup. A small team of talented engineers can build a minimum viable product on AWS, acquire initial customers through developer community engagement and product-led growth, and scale to significant revenue before needing traditional enterprise sales infrastructure. Venture capital has flooded the space with funding, creating an environment where new startups emerge constantly.
Wiz's ascent from founding to a reported twelve-billion-dollar-plus valuation in roughly four years illustrates how quickly a well-positioned newcomer can capture market share. However, distribution remains a significant barrier. Selling to enterprise security teams requires trust, track record, and channel partnerships that take years to build. The trend toward vendor consolidation, with enterprises seeking to reduce the number of security tools they manage, creates an additional barrier for new entrants that lack the breadth to compete as platform vendors.
The bargaining power of suppliers is low. Cloud infrastructure, the primary input for SaaS security companies, is commoditized across AWS, Azure, and Google Cloud Platform.
Talent is the key constrained input. Security engineers and researchers are expensive and competitive to recruit, but the talent market, while tight, is not controlled by a small number of suppliers.
The bargaining power of buyers is high and increasing. Enterprise security teams face an embarrassment of riches when it comes to vendor choices, and the proliferation of options gives them significant leverage in negotiations. Security budgets, while generally growing, are under increasing scrutiny from CFOs demanding clear return on investment. The trend toward platform consolidation means that buyers are actively seeking to reduce vendor count, which favors large platform players at the expense of mid-tier vendors like Rapid7. Switching costs exist but are declining as cloud-based architectures make it easier to swap tools than legacy on-premises deployments did.
The threat of substitutes is high. This is perhaps the most significant structural force working against Rapid7, and it deserves special attention because it is often underappreciated.
The most dangerous substitution threat comes not from direct competitors but from platform vendors that bundle security capabilities into broader offerings. Microsoft's inclusion of security features in its E5 enterprise licensing is the most prominent example. When a customer can get "good enough" SIEM, endpoint protection, and vulnerability assessment as part of a license they are already paying for, the value proposition of a standalone security vendor becomes harder to justify.
Cloud providers offering native security tools further erode the addressable market. Amazon Inspector for vulnerability scanning, Google Security Command Center for cloud posture, Azure Security Center for workload protection. None of these are as feature-rich as dedicated products, but they are free or nearly free with cloud consumption, and for many organizations, "good enough and free" beats "better but expensive."
Competitive rivalry is very high, and this is the force that most directly shapes Rapid7's daily reality. The cybersecurity market features dozens of well-funded competitors across every product category, intense price competition, rapid feature parity, and costly marketing battles for mindshare.
Consider the scale disparity. CrowdStrike, with roughly four billion dollars in annual revenue, invests more in sales and marketing alone than Rapid7 generates in total revenue. Palo Alto Networks, with over seven billion in revenue, can afford to acquire entire companies to fill product gaps the way Rapid7 acquires individual features. The M&A consolidation wave has created these larger, better-capitalized competitors, and the gap between the leaders and the mid-tier players like Rapid7 widens every year.
Examining the company through Hamilton Helmer's Seven Powers framework reveals a mixed picture.
Switching Costs are moderate. Rapid7 has real stickiness embedded in the integration of its products into customer security workflows, data history, and operational processes. A customer running InsightVM and InsightIDR has configured dashboards, established alert rules, built playbooks, and trained their team on Rapid7's interface. Ripping all of that out is costly and risky. However, cloud architectures have made this switching easier than it was in the on-premises era, and the trend toward API-based interoperability further reduces lock-in.
Network Effects are limited but real through the Metasploit community. The framework's value increases as more contributors add exploits and modules, and the community creates a self-reinforcing ecosystem of training, content, and expertise. The threat intelligence capabilities also improve with customer scale, as more customers provide more telemetry that improves detection accuracy. But these are not the kind of strong, direct network effects that create winner-take-all dynamics.
Scale Economies provide moderate benefit. Rapid7's cloud infrastructure costs improve with scale, and the threat intelligence and research operations benefit from being amortized across a larger customer base. But these scale advantages are not sufficient to create a durable moat on their own, particularly when competitors like CrowdStrike and Palo Alto Networks operate at significantly greater scale.
Branding is moderate. Metasploit gives Rapid7 authentic practitioner credibility, and the company is a recognized name in vulnerability management. But the brand is not as powerful as category creators like CrowdStrike in endpoint detection or Palo Alto Networks in network security. The brand carries less weight with C-suite buyers than it does with practitioners, which limits its value in large enterprise sales.
Counter-Positioning, which was a real advantage when Rapid7 was positioning cloud-native products against on-premises incumbents, has faded as competitors have caught up and Rapid7 itself now carries legacy technology debt.
Cornered Resources are weak. The Metasploit community is a unique asset, but the company does not control exclusive data, technology, or talent pools that competitors cannot access.
Process Power is developing through managed services operational capabilities, but has not yet reached the point of creating a sustainable competitive advantage.
The overall assessment is sobering but nuanced. Rapid7 is a good business with real revenue, real customers, and real capabilities, but it lacks a dominant competitive power that creates a durable moat. The company must continuously execute on product, sales, and M&A to maintain its position, a dynamic that is characteristic of what Helmer would call a "good business, not a great business."
Compare this to CrowdStrike, which built genuine counter-positioning by being the first major endpoint security vendor to go all-in on cloud-native, agent-based architecture when incumbents like Symantec and McAfee were anchored to their on-premises models. CrowdStrike's switching costs are exceptionally high because replacing an endpoint agent across hundreds of thousands of devices is a massive operational undertaking. CrowdStrike also benefits from strong network effects, as every customer's threat telemetry improves the platform's AI models for all customers. Rapid7 has some of these dynamics, particularly in the Metasploit community and threat intelligence, but not at the same intensity or scale.
For investors, this analysis suggests that Rapid7's valuation should reflect a discount to companies with stronger structural advantages. The current stock price, which implies a market cap of less than half the company's annual revenue, may be pricing in a degree of pessimism that underestimates the stickiness of the existing customer base and the value of the managed services franchise. Or it may be accurately reflecting a business that lacks the structural competitive advantages needed to reignite growth in an increasingly consolidated market.
XIII. Bull versus Bear Case
The investment debate around Rapid7 in early 2026 is unusually polarized, reflecting genuine uncertainty about whether the company can reignite growth or whether it is trapped in a slow decline.
The bull case rests on several pillars.
First, the company's existing customer base represents a foundation of recurring revenue that is more durable than the stock price suggests. Security products have high retention rates because the cost and risk of switching mid-contract are substantial. A company does not casually rip out its SIEM or vulnerability management platform, both of which are wired into dozens of other systems and processes.
Second, the managed detection and response business is growing and addresses a genuine market need. Most organizations cannot staff and operate a full security operations center internally, and MDR provides a solution that is sticky, recurring, and differentiated by human expertise rather than pure technology.
Third, the activist pressure from Jana Partners, while disruptive, may ultimately force the operational discipline and strategic focus that the company has lacked. The addition of new board members could bring fresh perspectives and greater accountability.
Fourth, the free cash flow generation, one hundred and fifty-four million dollars in 2024, demonstrates that the business can produce meaningful returns even in a low-growth environment. A company generating that level of cash at this valuation presents an interesting risk-reward profile if growth can be stabilized.
Fifth, the private equity interest that has periodically surfaced provides a potential floor on the stock price, as buyout firms recognize the strategic value of the customer base, the recurring revenue, and the managed services platform.
The bear case is equally compelling.
First, Rapid7 is caught in the "middle" of the cybersecurity market, lacking the scale of CrowdStrike and Palo Alto Networks, the cloud-native purity of Wiz, the category dominance of Tenable in vulnerability management, and the platform ubiquity of Microsoft. Being a generalist without leadership in any single category is a structurally disadvantaged position.
Second, the product portfolio remains too broad relative to the company's ability to invest in each product. Competing simultaneously in vulnerability management, SIEM, cloud security, application security, threat intelligence, and managed services spreads engineering and sales resources thin.
Third, cloud-native competitors have better product-market fit with the next generation of buyers. Organizations building on cloud-native architectures from scratch gravitate toward tools designed for those environments, not tools that evolved from on-premises roots.
Fourth, the platform bundling strategy being executed by Microsoft, CrowdStrike, and Palo Alto Networks is structurally disadvantageous for Rapid7. When a larger vendor can include "good enough" vulnerability management or SIEM as part of a broader platform deal, the standalone value of Rapid7's individual products diminishes.
Fifth, the near-flat revenue trajectory and the 2026 guidance suggesting a slight decline raise the specter of a business that is not just slowing but potentially shrinking, a trajectory that is extraordinarily difficult to reverse in enterprise software. In the SaaS world, once a company begins losing net new ARR, the compounding effect works in reverse: fewer new customers mean less expansion revenue, which means less investment in product and sales, which means even fewer new customers. Breaking out of this negative cycle requires either a transformative product innovation or a fundamental restructuring of the business.
There is also a myth versus reality dynamic worth addressing. The consensus narrative in early 2026 is that Rapid7 is a "broken" company in terminal decline. The reality is more nuanced. The company generates eight hundred and sixty million in revenue and over one hundred and fifty million in free cash flow. The customer base is not disintegrating. The products, while not category-leading, are functional and serve genuine security needs. The stock price reflects not a business in freefall but a market that has brutally repriced the company's growth prospects. The delta between "broken company" and "fairly-valued slow-growth cash generator" is enormous, and where you come down on that question determines whether the current valuation represents a compelling opportunity or a value trap.
The tension between these cases hinges on a small number of measurable outcomes. The two metrics that matter most for tracking Rapid7's trajectory are net revenue retention rate and product attach rate. Net revenue retention, which measures how much existing customers spend year over year including expansion, contraction, and churn, reveals whether the platform strategy is generating genuine cross-sell value or whether customers are consolidating away. Product attach rate, the percentage of customers using multiple Rapid7 products, indicates whether the platform vision is resonating or whether the company remains a collection of point solutions. These two metrics together capture both the health of existing customer relationships and the company's ability to expand its footprint within accounts, the fundamental levers that will determine whether Rapid7's story ends in turnaround or decline.
XIV. Epilogue and Reflections
Step back and consider the arc of this story. A company born on the Boston commuter rail in 2000, founded by three engineers who believed they could make vulnerability scanning better and cheaper. A pivotal acquisition in 2009 that gave the company a soul, the hacker credibility that money cannot buy. A cloud transformation that consumed the better part of a decade and hundreds of millions in investment. A stock that soared to one hundred and forty dollars and then collapsed to six. An activist investor demanding change. A board in flux. And through it all, a technology that the world genuinely needs, because the attackers never stop.
The Rapid7 story is, in many ways, the story of enterprise software itself over the past quarter century.
What makes Rapid7's journey particularly instructive is not that the company failed. It has not failed. With eight hundred and sixty million dollars in revenue, one hundred and fifty million in free cash flow, and a customer base that spans thousands of organizations, Rapid7 is a substantial business that delivers real value. What makes it instructive is the gap between what the company achieved and what the market once believed it could become. At its peak valuation, investors were pricing Rapid7 as if it would become a dominant security platform. The subsequent decline reflects not a business that collapsed but a narrative that proved more aspirational than the reality could sustain.
The comparison to successful transitions is illuminating. Microsoft's Azure pivot succeeded because the company had an existing distribution advantage in the form of enterprise agreements covering virtually every Fortune 500 company, deep relationships with CIOs and IT departments built over decades, and a balance sheet that could absorb billions in investment before the cloud business became self-sustaining. Satya Nadella could afford to be patient because Microsoft had Windows and Office generating massive cash flows to fund the transition.
Adobe's Creative Cloud transition worked because the company had dominant, near-monopoly market share in creative design tools. Photoshop, Illustrator, and InDesign had no comparable alternatives at the time, so converting the installed base from perpetual licenses to subscriptions was painful for customers but ultimately unavoidable. They grumbled, but they paid.
Rapid7 lacked both of these advantages. It was never the category leader in vulnerability management; Tenable held that position with Nessus installed in more organizations worldwide. And it was not the incumbent with unmatchable distribution; Microsoft and CrowdStrike had that advantage in their respective domains. Attempting a platform transition from a position of competitive parity, rather than dominance, is exponentially harder. You cannot afford to stumble because you do not have the cushion of category leadership to absorb the impact.
The timing dimension is crucial. Rapid7 was in the right place at the right time in the early 2000s, when vulnerability management was a nascent category with enormous growth potential. The Metasploit acquisition was perfectly timed, catching the project at a moment when it needed institutional backing to scale but before its value was fully recognized by the market. But the cloud transition, while directionally correct, arguably came too late to establish Rapid7 as a cloud-native leader and too early to avoid the pain of maintaining dual product lines during the transition.
The broader lesson about timing in technology is that being early is expensive and being late is fatal, and the window of "just right" is narrower than anyone would like. Rapid7 spent years and hundreds of millions of dollars building the Insight Platform, and by the time it was fully realized, the market had already moved on to the next wave of innovation, cloud-native architectures, AI-driven security operations, and platform consolidation by the biggest players.
As for what comes next, the possibilities range widely. The activist pressure could ultimately lead to a sale, either to a private equity firm looking for a security platform to build upon, or to a larger technology company seeking to bolt on vulnerability management and detection capabilities. A company like Cisco, which acquired Splunk for twenty-eight billion dollars in 2024, might find Rapid7's MDR capabilities and mid-market customer base a natural complement. Or a private equity firm could acquire the company at a significant discount to its historical peak, cut costs further, and attempt to sell it at a higher multiple once growth stabilizes.
The company could also execute a successful turnaround under its current structure, focusing on MDR and a streamlined product portfolio, and rebuilding growth from the managed services foundation. Or it could remain in the uncomfortable middle ground, generating cash but not growing, slowly losing relevance as the market evolves around it.
What is certain is that the cybersecurity market will continue to evolve at a pace that punishes complacency and rewards reinvention. The threats are not getting simpler; ransomware, nation-state attacks, and AI-enabled phishing have made the threat landscape more dangerous than at any point in history. The architectures are not getting less complex; multi-cloud, edge computing, and the explosion of IoT devices have expanded the attack surface beyond anything the founders of Rapid7 could have imagined when they were sketching product ideas on the commuter rail in 2000.
And the demand for security, real security, not just compliance checkboxes, has never been higher. Rapid7's ability to deliver on that demand, in whatever form the company takes in the years ahead, will determine whether its story is remembered as a cautionary tale about the limits of enterprise software transitions, or as the first act of a longer story about reinvention and resilience.
XV. Resources for Further Reading
For those interested in going deeper into the Rapid7 story and the dynamics of the cybersecurity market, the following resources provide valuable context.
The Rapid7 S-1 filing from 2015 offers a snapshot of the company's pre-cloud platform ambitions, its competitive positioning at the time of the IPO, and the financial profile of a mid-stage security company preparing for public markets. Reading it alongside the company's most recent annual reports reveals how dramatically the strategy and financial profile have evolved.
HD Moore's original writings and presentations about the Metasploit Project provide essential context for understanding the community dynamics and technical foundations that made the acquisition so transformative. The ongoing Metasploit Framework documentation on GitHub remains one of the most comprehensive resources for understanding penetration testing methodology.
Gartner's Magic Quadrant reports for Vulnerability Management and SIEM, tracked over multiple years, illustrate Rapid7's shifting competitive position relative to Tenable, Qualys, CrowdStrike, and other players. The progression of these reports mirrors the company's strategic evolution from point solution to platform.
Clayton Christensen's "The Innovator's Dilemma" provides the theoretical framework for understanding Rapid7's cloud transition challenges. Geoffrey Moore's "Crossing the Chasm" explains the enterprise security sales dynamics that Rapid7 navigated during its growth phase. Both are essential reading for understanding why the company made the strategic choices it did, and why those choices were both necessary and insufficient.
Battery Ventures' annual "State of Cloud Security" reports and the security market maps published by firms like Redpoint Ventures and Costanoa Ventures offer broader industry context that illuminates the competitive dynamics shaping Rapid7's future.
For those interested in the private equity dynamics, the public filings and press coverage surrounding the Thoma Bravo acquisition of Darktrace in 2024 provide a useful comparison point, illustrating how PE firms evaluate and restructure cybersecurity companies. The Jana Partners 13D filings with the SEC offer direct insight into the activist's thesis for value creation at Rapid7.
Finally, Rapid7's own research publications, vulnerability disclosures, and Metasploit community contributions remain a window into the technical culture that has sustained the company through multiple reinventions. The annual Rapid7 Under the Hoodie report, which publishes findings from thousands of real-world penetration tests, is both an educational resource and a testament to the practitioner credibility that the Metasploit acquisition created nearly two decades ago.
 Chat with
this content: Summary, Analysis, News...
Chat with
this content: Summary, Analysis, News...
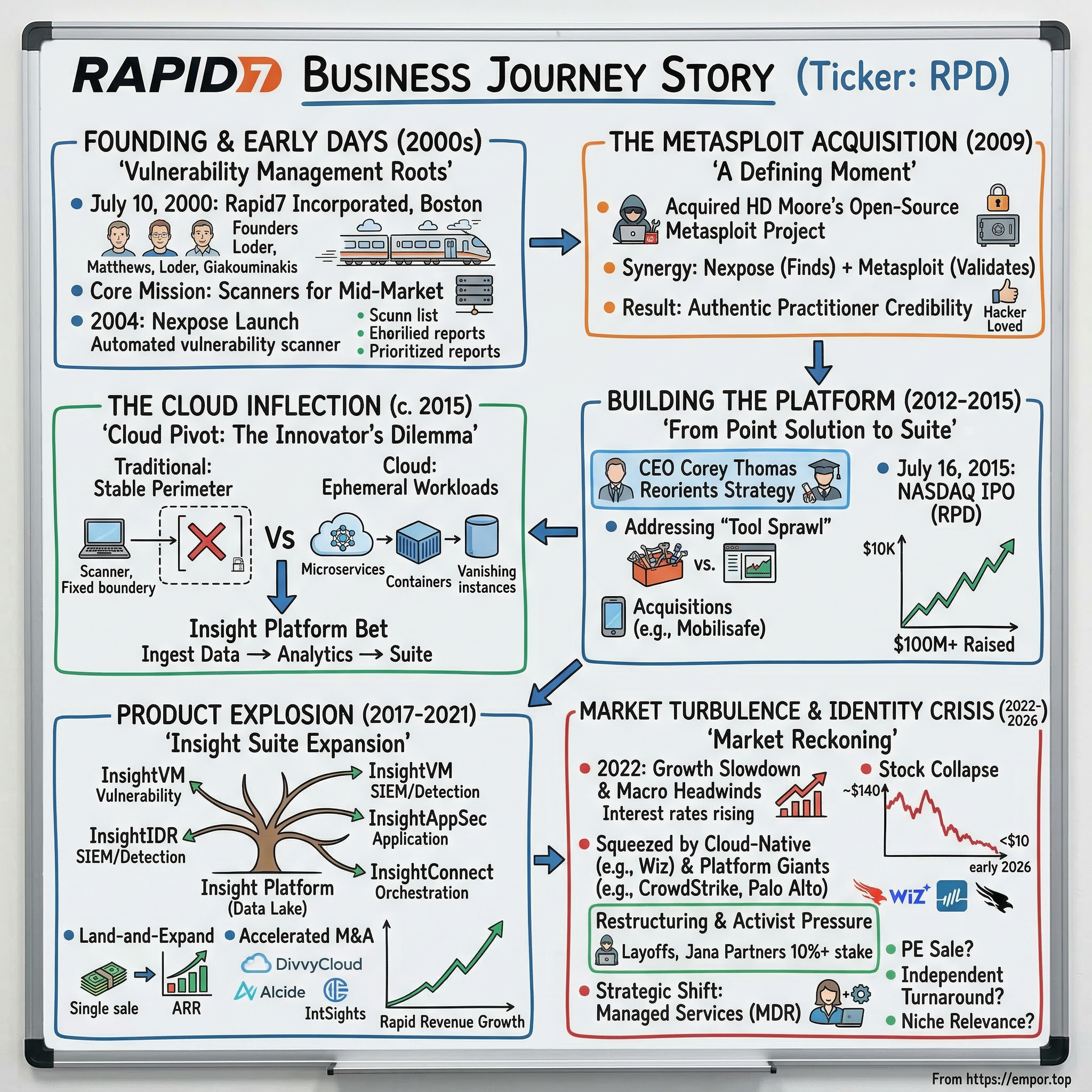
 Amazon Music
Amazon Music